System.Object.GetHashCode()
After reading Ayende’s blog about GetHashCode file about the pitfalls of GetHashCode.
I’ve coded it in a Java class but have yet to apply it anywhere else.
I don’t believe I’ve used any objects as keys in my applications. I mainly use value objects. From a friend, I’ve heard that .NET automatically prevents collisions by doing chaining (if two objects have the same hashcode, the values are link-listed off that key)
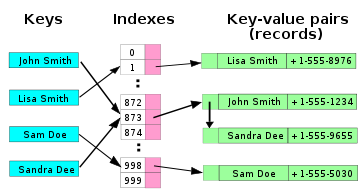
Image borrowed from Wikipedia